Open Source Sensitive Data Discovery

Pii tools comes with context sensitive ai detectors for gdpr ccpa phi pci and more.
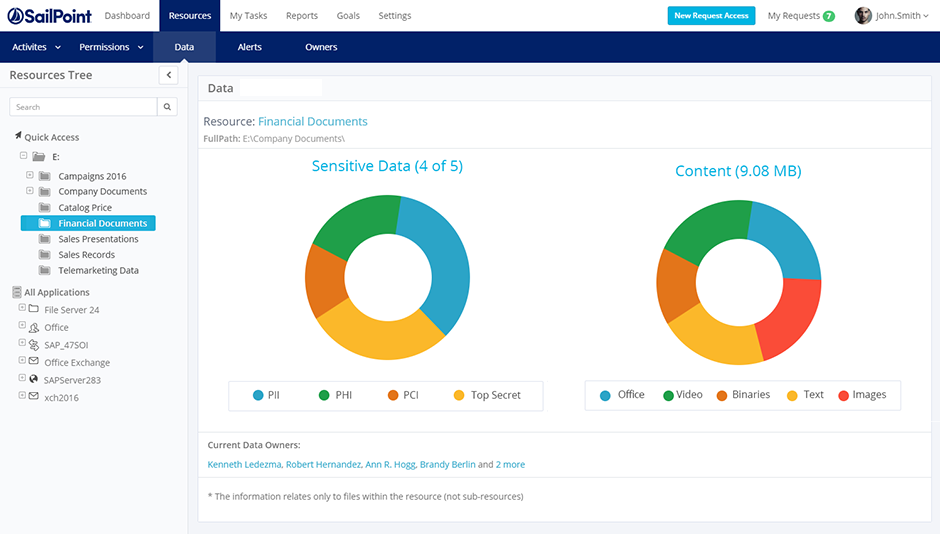
Open source sensitive data discovery. You ve got sensitive data. Sensitive data discovery and achieving compliance is made possible with ground lab s unique software and tools. Track information across your network including file shares san and nas storage and sharepoint sites. Search engine like tools are a niche category in data discovery.
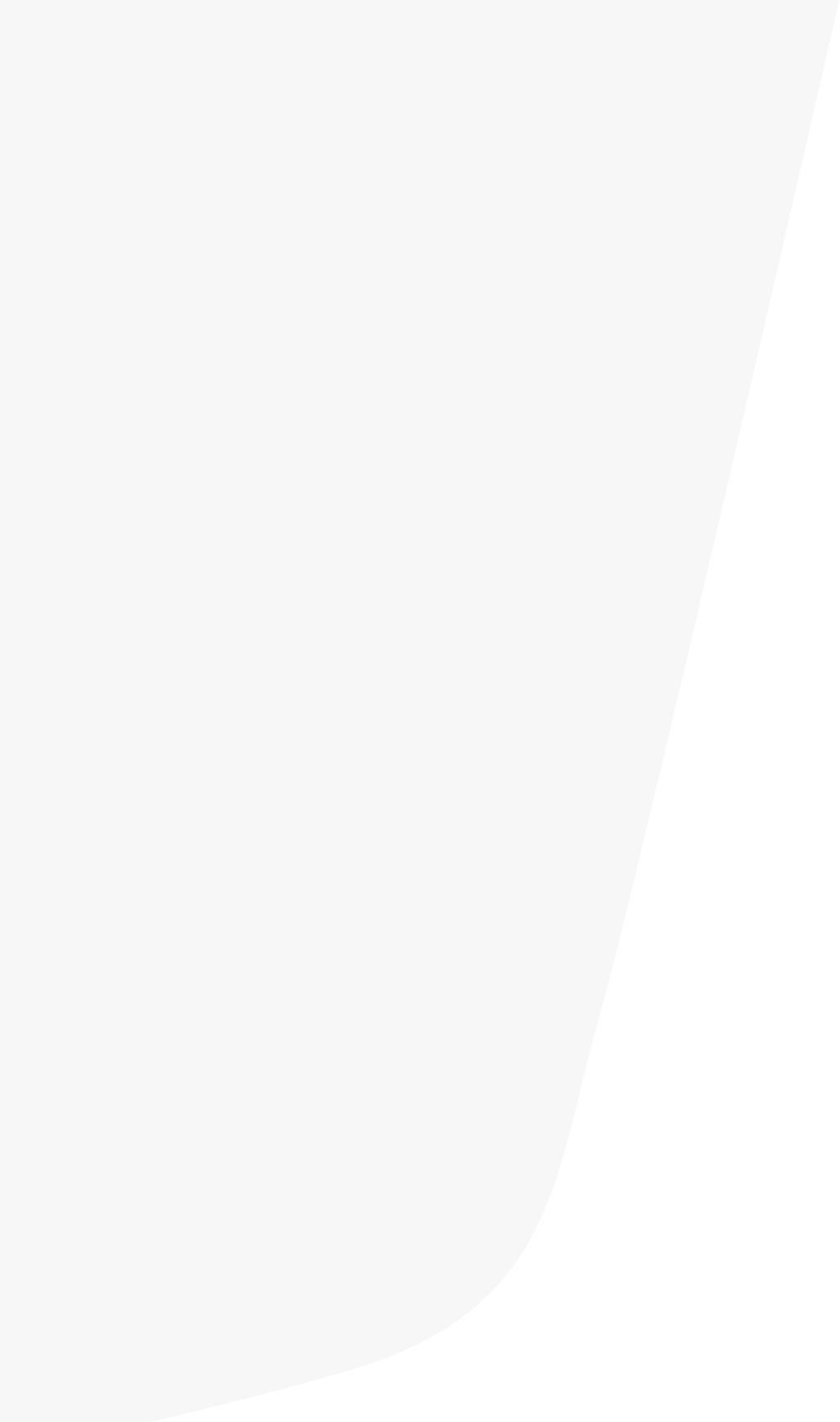
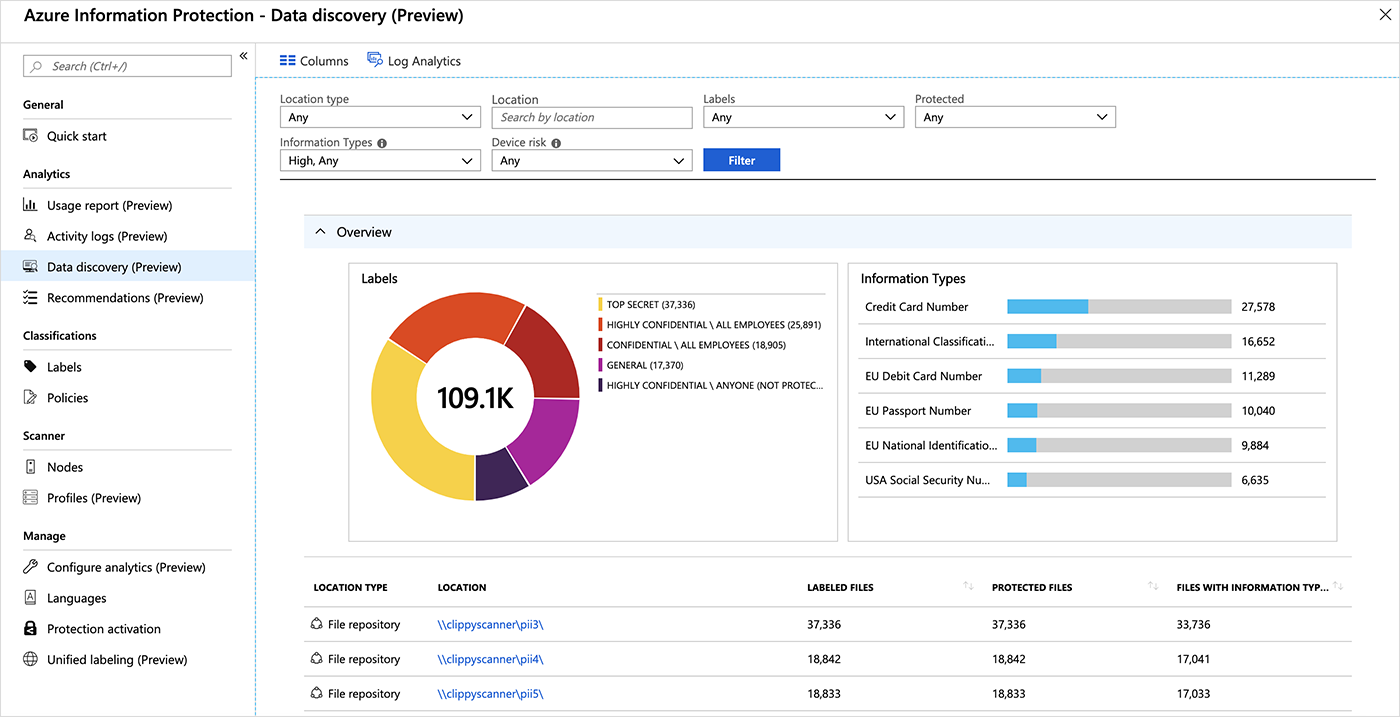
Data classification engine gives context around sensitive data so that you can easily identify and lock down overexposed data stale data and remediate security vulnerabilities. They re specifically for performing keyword searches of large collections of files and they feature an interface similar to that of web search engines such as google and bing. Varonis automatically scans and classifies sensitive regulated information stored in file shares nas devices sharepoint and office 365. Remember that on version 3 0 all configuration for data discovery is stored on database.
But it can also be customized to have custom data classifiers. There are lots of high end products that will automate the process of data discovery but it doesn t take much effort to hunt down data yourself. Kogni has pre built data classifiers that already understand and detect sensitive data. Sensitive data discovery is the key to a great data security strategy.
Kogni is capable of detecting your sensitive data from any kind of data source. Check out this list of sensitive data discovery tools and choose the one that is the best fit for your organization s needs. Remediate compliance breaches in real time. Data discovery will perform an nlp scan an regex scan or dictionary scan of data in the database and return columns that have a match score greater than the value of probability threshold specified in parameters.
Scroll down for pii tools. The secret behind spirion data platform s highly accurate sensitive data discovery software solution is our anyfind technology. Java jar redatasense jar database discovery d note. Trust the companies that trust us.
The era of clumsy regexps is. Quarantine delete or revoke access to exposed data. It all starts with accurate discovery of data sources. Structured unstructured or semi structured.
Introducing a world without manual discovery. Understanding what and where sensitive information is allows you to set appropriate levels of control in your data discovery process.